
Transnational Conflict Prevention and Interdiction Programmes
Appropriate Use
|
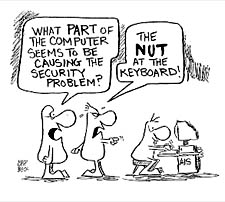
| This topic
discusses rules for using your computer. You should also read Computer Vulnerabilities,
which describes in nontechnical language the security and other vulnerabilities of
computer networks that make some of these rules necessary. Owing to the magnitude of problems that can be caused by misuse of computer systems, Misuse of Technical Information Systems is now one of the 13 criteria used in adjudicating approval and revocation of security clearances for access to classified information. |
 |
Many aspects of computer use are governed by your organization's policy rather than by federal government regulation. Many government agencies and defense contractors specify the security procedures and prohibited or inappropriate activities discussed below.
The following are basic rules for the secure use of the computer.
Many offices permit some, minimal personal use of office equipment when such personal use involves minimal expense to the organization, is performed on your personal non-work time, does not interfere with the office's mission, and does not violate standards of ethical conduct.
The following activities are considered to be misuse use of office equipment:
There are two big problems with e-mail. One is increased risk of accidental security compromise. The other is sending inappropriate materials by e-mail, which has caused many people to be fired from their jobs.
Security Risks with E-Mail
As a result of the Internet and e-mail, there has been a sharp increase in security incidents involving the accidental disclosure of classified and other sensitive information. One common problem occurs when individuals download a seemingly unclassified file from a classified system, and then fail to carefully review this file before sending it as an attachment to an e-mail message. Too often, the seemingly unclassified file actually has some classified material or classification markings that are not readily apparent when the file is viewed on line. Sending such material by e-mail is a security violation even if the recipient has an appropriate security clearance, as e-mail can easily be monitored by unauthorized persons. See E-Mail Pitfalls in Computer Vulnerabilities.
More important, even if the downloaded file really is unclassified, the electronic version of that file may have recoverable traces of classified information. This happens because data is stored in "blocks." If a file does not take up an entire block, the remainder of that block may have recoverable traces of data from other files. (See Security of Hard Drives for further explanation of this problem.) Your system administrator must follow an approved technical procedure for removing these traces before the file is treated as unclassified.
Some organizations have found it necessary to lock their computer drives to prevent any downloading of files from the classified system. If an individual wishes to download and retransmit an unclassified file from a classified system, the file must be downloaded and processed by the system administrator to remove electronic traces of other files before it is retransmitted.
Inappropriate Materials
Sending e-mail is like sending a postcard through the mail. Just as the mailman and others have an opportunity to read a postcard, network eavesdroppers can read your e-mail as it passes through the Internet from computer to computer. E-mail is not like a telephone call, where your privacy rights are protected by law.
The courts have repeatedly sided with employers who monitor their employees' e-mail or Internet use. A 2005 survey found that 63% of corporations with 1,000 or more employees either employ or plan to employ staff to read or otherwise analyze outbound email. 27% of the companies reported terminating an employee due to email misuse during the previous year. 35% investigated a suspected email leak of confidential information during the past year. In addition to protection of their intellectual property, companies were concerned about compliance with financial disclosure regulations.4 Organizations also monitor email to protect themselves against lawsuits, as the organization can be held liable for abusive, harassing, or otherwise inappropriate messages sent over its computer network.
In the past couple years, The New York Times fired 23 employees for exchanging off-color e-mail. Xerox fired 40 people for inappropriate Internet use. Dow Chemical fired 24 employees and disciplined another 230 for sending or storing pornographic or violent material by e-mail. 1
Several years ago, Chevron Corp. had to pay $2.2 million to plaintiffs who successfully brought a suit of sexual harassment, in part because an employee sent an e-mail to coworkers listing the reasons why beer is better than women. 2
Secrets in the computer require the same protection as secrets on paper. Information can be recovered from a computer hard drive even after the file has been deleted or erased by the computer user. It is estimated that about a third of the average hard drive contains information that has been "deleted" but is still recoverable. 3
When you delete a file, most computer operating systems delete only the "pointer" which allows the computer to find the file on your hard drive. The file itself is not deleted until it is overwritten by another file. This is comparable to deleting a chapter heading from the table of contents of a book, but not removing the pages on which the chapter is written. Some networks may be configured to "wipe" or purge the hard drive when information is deleted, but most are not.
Computers on which classified information is prepared must be kept in facilities that meet specified physical security requirements for processing classified information. Special procedures may also be appropriate when working with some types of sensitive unclassified information. At a minimum, special procedures for clearing hard drives are appropriate prior to disposing of old computers on which sensitive information has been prepared.
Check with your security office concerning rules for traveling with a laptop on which sensitive information has been prepared. Laptop computers are a particular concern owing to their vulnerability to theft.
Passwords are used to authenticate an individual’s right to have access to certain information. Your password is for your use only. Lending it to someone else is a security violation and may result in disciplinary action against both parties. Never disclose your password to anyone. Memorize it – do not put it in writing. If you leave your terminal unattended for any reason, log off or use a screen lock. Otherwise, someone else could use your computer to access information they are not authorized to have. You will be held responsible if someone else uses your password in connection with a system transaction.
Do change your password regularly. Use a password with at least six and preferably eight characters and consisting of a mix of upper and lower case letters, numbers, and special characters such as punctuation marks This mix of various types of characters makes it more difficult for a hacker to use an automated tool called a "password cracker" to discover your password. Cracking passwords is a common means by which hackers gain unauthorized access to protected systems.
For additional information on selecting a strong password and why this is so important, see Passwords and the case studies in Computer Vulnerabilities.
"Social engineering" is hacker-speak for conning legitimate computer users into providing useful information that helps the hacker gain unauthorized access to their computer system.
The hacker using social engineering usually poses as a legitimate person in the organization (maintenance technician, security officer, inexperienced computer user, VIP, etc.) and employs a plausible cover story to trick computer users into giving useful information. This is usually done by telephone, but it may also be done by forged e-mail messages or even in-person visits.
Most people have an incorrect impression of computer break-ins. They think they are purely technical, the result of technical flaws in computer systems which the intruders are able to exploit. The truth is, however, that social engineering often plays a big part in helping an attacker slip through security barriers. Lack of security awareness or gullibility of computer users often provides an easy stepping stone into the protected system if the attacker has no authorized access to the system at all.
For additional information see "Social Engineering" and the two case studies in Computer Vulnerabilities.
Laptop computers are a prime target for theft for the value of the information on them as well as for the value of the computer. According to Safeware, a computer insurance firm in Columbus, Ohio, 309,000 laptop computers were stolen in the United States during 1997. There is also a high risk of theft during foreign travel. See Theft of Laptops and Theft While Traveling.
The best protection for information on your laptop is to encrypt all sensitive files and e-mail. A variety of keys, cards, and other physical means of preventing unauthorized access to information on a laptop are now coming on the market. Evaluate the various alternatives to see if one of them meets your needs.
Here are some other guidelines for protecting laptops:
Never let a laptop out of your sight in an airport or other public area. If you set it down while checking in at the airport counter or hotel registration desk, lean it against your leg so that you can feel its presence, or hold it between your feet.
When going through the airport security check, don't place your laptop on the conveyor belt until you are sure no one in front of you is being delayed. If you are delayed while passing through the checkpoint, keep your eye on your laptop.
Never, ever, check your laptop (or other valuables) with your luggage.
Never keep passwords or access phone numbers on the machine or in the case.
If possible, put your laptop in a bag that does not resemble a laptop carrying case.
If your hotel room has a safe, keep your laptop in the safe while you are out of the room.
Before traveling, back up all files.
Do not view sensitive material on your laptop while in a public place, especially not in an airplane. It is common practice for your airplane seatmate to look at what is on your screen.
If you access your office network from home or do work at home that is then emailed to the office or brought to the office on any removable storage media, this can affect the security of the office network. You have an obligation to take standard procedures for protecting your home computer against viruses and other problems that might be transmitted to your office network. These include installing a virus checker with automatic updates, installing a personal firewall, turning off or uninstalling any options that significantly increase security risk, and keeping your computer's operating system up-to-date with security fixes as they become available.
Related Topics: Computer Vulnerabilities, The Insider Threat to Information Systems.
References
1.
Larry
Armstrong, "Someone to Watch Over You," Business Week, July
10, 2000, p. 189. Todd R. Weiss, "Dow Fires More Employees Over
Inappropriate E-Mails." CNN.com, September 19, 2000.
2. Anna Davison, "Is Your E-Mail Being
Monitored?" Monterey County Herald, July 29, 2000, p. E1.
3. Alex Markels, The messy business of culling company
files. The Wall Street Journal, May 22, 1997, p. B1
4. Proofpoint,
Outbound
Email Security and Content Compliance in Today's Enterprise, 2005. A
copy of this survey may be ordered at www.proofpoint.com/outbound/.
HOME | PROTECTING UNCLASSIFIED CONTENTS | TOP OF PAGE | HELP
INFORMATION
| CONDUCT | THREATS | TECH
VULNERABILITY | ASSISTANCE
SPY STORIES | TREASON
101